DefCon 22 | DISOBEY!
 The word, “Hacker” automatically instills a sense of fear and mistrust in most people. You might imagine some dark, shadowy nefarious character in a black hat, trenchcoat and possibly donning a Guy Fawkes mask. Or there’s always the popular mid-90s flick featuring phreaks on roller-blades rampaging through metropolitan New York. Whatever your perception may be, an estimated 15,000 attendees showed up for this year’s DefCon 22, an annual event with talks, contests, vendor-booths, charities, workshop training areas and more.
The word, “Hacker” automatically instills a sense of fear and mistrust in most people. You might imagine some dark, shadowy nefarious character in a black hat, trenchcoat and possibly donning a Guy Fawkes mask. Or there’s always the popular mid-90s flick featuring phreaks on roller-blades rampaging through metropolitan New York. Whatever your perception may be, an estimated 15,000 attendees showed up for this year’s DefCon 22, an annual event with talks, contests, vendor-booths, charities, workshop training areas and more.
The Badge
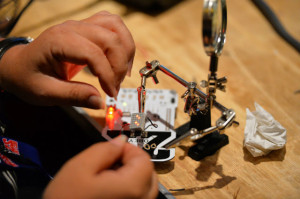
Upon entering most every conference, attendees are normally offered a name-tag or some other such identifier to indicate that they have paid for admission. Since this is a hacker convention, DefCon takes it to the next level with a series of re-programmable and modifiable computer-board badges. Each contains a microprocessor, LED lights, perhaps an infrared receiver, micro-USB port and multiple slots to solder in any additions and upgrades. Two contests in particular focused on the badge, one was for the best counterfeit badge and another for the best badge-hack. Pictured here is the winner of the badge-hacking contest, a badge that was converted to a flying drone by billy, loather, and kennedse.
Talks
Talks at DefCon are mostly focused on topics in information security, some with very practical real-world applications and implications. For example, how safe would you feel if you found out that hackers might be able to remotely access and control the steering wheel and brakes in your car? Or what if you found out that it’s possible for hacker terrorists to disrupt 911 calls when emergency services might be needed most? Terrifying as these examples may sound, the exact purpose of these discussions is to address and seek solutions to such flaws in security. Simply burying your head in the sand is not going to make the problem go away.
Perhaps the most notable “celebrity” talk came from John McAfee, founder of McAfee anti-virus. A legend in the industry; his story is a good example of the outlandish and eccentric personalities one might encounter at DefCon. At 68 years old, McAfee makes no apologies for dating a 17r-old girlfriend and recounted a story of now being half-deaf after being shot at in the head by her. He went further to say that his life is currently being threatened by the government of Belize and he’d be dead if not for the 17,000+ hours evidence he possesses detailing corruption within the Belizean Cabinet.
Villages
More than just dry lectures though, DefCon provides an opportunity to attend specialized workshops that provide hands-on experience in subjects such as social engineering, lock-picking, packet-hacking, tamper-evident security and more.
Yes, DefCon is family-friendly. r00tz Asylum is a special area of DefCon for children to learn about “white-hat hacking,” using their creative minds to find solutions to challenges while under the supervision of their parents/guardians. For safety purposes, the only adults allowed into this area are parents/guardians accompanied with children.
Vendors
From hacker stickers and t-shirts to handcuffs and lock-picking sets, the vendor area is to hackers a bit like what pleasure island is to Pinocchio. It’s interesting to see academic institutions like Carnegie Mellon offering courses in MSIS in close proximity to more hands-on booths such as Hard Case Survival specializing in surreptitious entry / restraint escape training for government and military.
Another “celebrity” of hacker-lore, Kevin Mitnick did a book-signing session at DefCon 22. Others like John “Captain Crunch” Draper tuned in remotely via social outlets.
Events
As DefCon is really a series of niche interests and communities that come together; there are special events that take place before, during, and afterhours. Here are a few examples:
Toxic BBQ – Slightly off the beaten path, toxic bbq normally brings together circles of hacker friends and family for an outdoor picnic on the first evening. Bring some meat or donate a few bucks, there’s always plenty of food and friendship to go around.
Mohawk-Con – Get your head buzzed at DefCon to support the Electronic Frontier Foundation, Hackers for Charity, and your favorite Hackerspaces!
Hackers for Charity is a non-profit organization that leverages the skills of technologists to help provide food, equipment, job training and computer education to the impoverished in Uganda. Pictured here is one of their projects, the Pelican Pi/Rugged Pi which is basically a raspberry pi microcomputer loaded with educational content (RACHEL, GCFLearnFree.org, KA-Lite) and housed within a secure unit. The raspberry pi acts as a library/repository that can track login profiles across wireless devices and this type of set-up allows a number of students to individually learn while sharing a limited number of laptops, tablets or cell-phones.
Contests
Further adding excitement and intrigue to DefCon are a number of various contests for players to match their skills against each other. Certain contests offer a grand prize of the coveted, “Uber” black badge which grants lifetime admittance to DefCon. Some examples include:
Spot the Fed – Hilarity. There’s a contest at DefCon where attendees are encouraged to keep a look-out for Federal Agents. Possibly at the beginning of a talk; the track manager might announce a round of “Spot the Fed” and will ask if anyone in the audience thinks they can point out a Federal official. People raise their hands and one person is selected. They now have a chance to point out the individual they suspect and both are then brought on stage for verification. If the accuser is correct, they win a “I spotted the Fed” t-shirt and the agent receives a “I am the Fed” t-shirt.
Scavenger Hunt – The Scavenger Hunt is the 2nd longest running contest in the history of DefCon where teams of up to 5 players compete for the most points in finding and completing various “challenges.” In addition to a paper list, teams were also given a 3.5″ floppy disk which contained a number of additional items as well as several cryptography puzzles. *Just fyi, a 3.5″ floppy disk is that icon you see in Microsoft Word when you press the “save” button.) The list includes such fun items as:
-zipline between opposing walls in the contest area
-Power Glove, in person
-modify a bike to operate a blender, provide beverages
-team member in storm trooper armor
-swim in an inflatable pool floating in a real pool
-install Gentoo. (Must show judge before starting and when completed.)
Capture the Flag
This is probably one of the most “elite” hacker tournaments in the world. Basically, various teams of hackers must protect their private servers while mounting attacks on others. Points are issued accordingly for various attacks and defenses with a major offensive in “stealing” another team’s flag while protecting your own. International teams must pre-qualify through solving sets of computational problems before DefCon and this showdown then lasts for 3 days, 8 hours a day. At the end, winners can really claim to be the “best of the best.”
Government
Indeed, it has been know that the NSA has been known to actively recruit from DefCon’s Capture the Flag challenge and it’s quite encouraging to see the Federal Trade Commission getting involved this year as well. The FTC launched a series of 3 contests at DefCon called ZAP RACHEL in an effort to combat illegal robocalls.
From the FTC’s press release, “The FTC receives more than one million consumer complaints about robocalls every year. Most of these complaints are against Rachel at Cardholder Services or one of her robotic minions … The pitches may vary but the punch line is always the same: “Press One to Learn More!” Of course, the problem of telephone spam is more than a mere annoyance, as fraudsters do succeed in pilfering private information – and money – from innocent people. At the same time, the related menace of telephone Denial of Service attacks is on the rise … That’s why law enforcement alone isn’t enough to solve the problem, and the FTC is investing in technical solutions that can help a growing community of experts do battle with robocallers.”
As a highlight at DefCon 22, the FTC is awarding $17,000 in cash prizes through this contest series.
Community
Hackers are not normal people. They’re weird and have a strange sense of humor. But are they malicious? Some might say that the “Wall of Sheep” is a bit sketchy, but at least several digits/characters are redacted to maintain privacy. A row of skilled volunteers monitor network traffic, capture people’s personal information through open airwaves and then posts this through a projector onto a large wall for all to see. You know that little pop-up you get whenever you log in at the coffee shop or local restaurant? The purpose of this area is more to reiterate the warning most people ignore when connecting to public networks. No, your information is not secure! Still, this is really more of a mischievous prank than anything truly malevolent.
In sharing a personal experience, I’ve been warned not to use any electronics while attending DefCon. I’ve been advised to go as far as to take the battery out of my mobile-phone for fear that “hackers” are going to steal my information. Indeed, I’ve learned it’s possible for someone to build a fake cell-phone tower and thus capture any of your personal data before re-routing it through. Ok, that’s pretty scary to know that there are people who are capable of such feats. Yet I’d like to believe in the best of people, as Phil recently mentioned: that “with great power comes great responsibility,” especially among hackers.
On the last night of DefCon, I decided to join in the festivities and went dancing down at the pool party, then over at the indoor dj area, a few private suite parties until I finally realized that I must have dropped my wallet somewhere. I know. It happens. Stay calm, don’t panic. And so I frantically retraced my steps everywhere, spoke with security guards and then at Lost & Found. But unfortunately nothing and then despair begins to set in. But what more could I do? Sitting down and taking my phone out, I saw several missed calls and text-messages while I was busy running around. My heart leapt for joy when a complete stranger returned my wallet fully intact. If you’ve ever lost your wallet before, you know what a sad and sinking feeling it can be. Imagine my gratitude and utter faith in humanity restored.
Remember, hackers are more like MacGyver who figure out solutions to problems. They see a challenge and immediately set their minds to solving a puzzle. There are the good guys out there who help you too.
High-Resolution photos by DEFCON/HACKERPHOTOS.COM