Lessons in Car Hacking at Def Con 24
 I grew up with some pretty strict parents. And when I inherited my first car, a 1987 tan/gold Volvo 740GLE that was built like a tank, they would check and monitor my mileage quite closely. They knew how far the commute to college was, what it should take to do local trips from my dorm to the grocery store or laundromat and basically kept me on a short leash. As a rambunctious young teenager with the newfound independence of living away from home, these limitations put a severe damper on my social life. Crowd-sourcing for a solution, I asked around and a fraternity buddy who was a bit of a car guy agreed to help. So on one sunny Sunday afternoon in the spring of ’98, we started taking apart panels and unplugged all sorts of wires and cables in testing the various components to see what they do. At some point, we broke off a clip and undid the plug that connected both the speedometer and odometer. Success! I wasn’t able to tell how fast I was going anymore but I figured that as long as I stayed within the flow of traffic, things should be ok. More importantly though, the miles did not register and I now had the liberty to roam wherever I wanted. This began my first foray into automotive hacking..
I grew up with some pretty strict parents. And when I inherited my first car, a 1987 tan/gold Volvo 740GLE that was built like a tank, they would check and monitor my mileage quite closely. They knew how far the commute to college was, what it should take to do local trips from my dorm to the grocery store or laundromat and basically kept me on a short leash. As a rambunctious young teenager with the newfound independence of living away from home, these limitations put a severe damper on my social life. Crowd-sourcing for a solution, I asked around and a fraternity buddy who was a bit of a car guy agreed to help. So on one sunny Sunday afternoon in the spring of ’98, we started taking apart panels and unplugged all sorts of wires and cables in testing the various components to see what they do. At some point, we broke off a clip and undid the plug that connected both the speedometer and odometer. Success! I wasn’t able to tell how fast I was going anymore but I figured that as long as I stayed within the flow of traffic, things should be ok. More importantly though, the miles did not register and I now had the liberty to roam wherever I wanted. This began my first foray into automotive hacking..


Things have come a long way in the past three decades though. At the Paris Motor Show 2016, Volkswagen announced a new 2018 electric vehicle model that will go 373 miles on a 15 minute charge AND cost less than the gas-powered version. New OEM Lucid Motors (formerly Atieva) has modified a Mercedes-Benz Metris Van that they’ve lovingly named Edna and this 900hp beast can roar from 0-60mph in just 2.74 seconds, beating out a Tesla Model S P90D, Ferrari California T, BMW i8 and Dodge Viper. Consider what they’ll be able to do for a more aerodynamic sedan on the way in 2018. Speaking of Tesla, Elon Musk’s plan to deliver 373,000 Model 3 vehicles by 2017 includes a fully-automated robotic factory nicknamed the Alien Dreadnought which will not have any human workers on the production line.
Yet with the introduction of such innovative technology, what’s being considered in terms of cybersecurity safety? As infotainment and connected services/internet features are more intricately wired into automotive systems, what’s to prevent malicious hackers from taking control of the steering wheel and simply driving it off the road? Epic movie spoiler alert, it can already be done.

Two years ago, I listened intently as Charlie Miller and Chris Valasek gave a talk at Def Con 22 about automotive software hacking. They spoke about their exploration into various ways that a “hacker” could gain access to the CanBus or ECU of a vehicle, the network and brain that talks to each component and tells it what to do. Last year, I heard the results of their further research and actually got to see them gain access into the vehicular network of a Jeep Grand Cherokee and then operate it by remote control with a laptop. I also saw a new area at Def Con, the first Car Hacking Village, decked out with a bunch of cars to check out and get a first-hand look at the various potential entry-points. This year, I saw the village expanded with a schedule of further specialized talks in their own “mini-conference,” demo tables for people to get hands-on experience working on various internal parts and sensors, sponsor presentation tables, more cars for people to physically see where to find the various instrument panels/compartments and Fiat Chrysler hooked up a Dodge Charger Hellcat to a life-sized monitor so that participants could sit behind the wheel in a fully-realistic simulator. Additionally, a separate area to buy hacker gear, the Vendor Village also included a Car Hacking booth where one could purchase actual tools, components and manuals to aid in accessing a vehicle network.





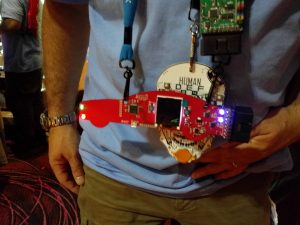
I got a chance to speak with Robert Leale of CanBusHack who along with Craig Smith are the main two masterminds and workhorses responsible for the Car Hacking Village at Def Con. Robert has been involved with car-hacking since high school in the mid 90s, basically just fixing up and modding his own personal car. Fast-forward to a career in reverse-engineering for aftermarket and OEM automotive companies, on a day-today basis, he conducts “competitive analysis” in figuring out how the various electronic systems work between different models and manufacturers. With help from Parsons as the first sponsor last year, he and Craig started the village as an area for people to come and explore the possibilities of what they can do with their cars. From high school buddies dropping their rides or adding an upgraded exhaust to reprogramming the unlock button on your key to also start the engine and turn on the radio at the same time, this is an open and safe space to intimately learn the minute details of a car.


I’ll admit that I was a bit intimidated at first. After all, I’m not a computer programmer myself and so I was a bit relieved to hear Robert tell me that no, you don’t actually need to know how to code or possess any prior automotive knowledge. Just sit down and mess around with the controls in sending different messages to various electronic components. Yes, of course there are more advanced courses as well and this is really a place for anyone who might have an interest in better understanding their car and how each and all of the different parts work together.


There are contests like Tanks for the Memories as well as a CTF tournament or “Capture the Flag” where each flag is a challenge. One “captures the flag” each time they’re able to find a solution to a challenge and the winner is the person or team who has captured the most flags. In recognition of the value that the Car Hacking Village brings, Def Con has started awarding a Black Badge for the CTF contest winner. (The highly coveted Black Badge allows a holder to attend any and all future Def Con events indefinitely!)
However, the Bug Bounty programs being run by BugCrowd might be the real gem of the village in providing a legitimate avenue for the Def Con car hacking audience to make a real-world impact. Fiat-Chrysler was this year’s chosen sponsor (last year was Tesla) in a program where security researchers are given the opportunity to granularly explore otherwise restricted automotive systems for any bugs they may find. Contest winners are then awarded various amounts and prizes normally range from $150-$1500 per new bug identified. Reflect upon that for a moment. As we delve into the depths of IoT and automotive connectivity further integrates with the World Wide Web, hackers are now being INVITED (if not actively recruited) to investigate internal car systems. Speaking with Jason Haddix at BugCrowd,
“We invite hackers to tell us about it by gamifying hacking. Come hack us. Through our program, we can waive legal liability to the researcher as they provide proof of concept exploits, etc in working with BugCrowd customers to find or suggest any mitigation that might prevent an attack. This is 100% net positive to both the automotive and researcher communities. Bugs get found, researchers aren’t afraid of getting prosecuted.”


With the White House backing of a massive effort to build an infrastructure network of electric vehicle charging stations across the United States and autonomous features already available in certain luxury cars today, the near future of transportation is clear. And with all of the advancements in infotainment and connectivity, a car is so much more than a vehicle that gets you from point A to point B. It’s a computer on wheels and car “hacking” is not so much about fantasy science-fiction spy games as it is simply about being able to reprogram your car to specifically do what you want.
“There are a lot of people that like to tinker with their vehicles or tinker with IT systems,” said Titus Melnyk, senior manager – security architecture, FCA US LLC. “We want to encourage independent security researchers to reach out to us and share what they’ve found so that we can fix potential vulnerabilities before they’re an issue for our consumers.”
P.S. I heard they’re working on an actual car as a giveaway for next year’s Car Hacking Village. See you at the 25th anniversary of Def Con in Las Vegas next year, July 27-30th, 2017!